
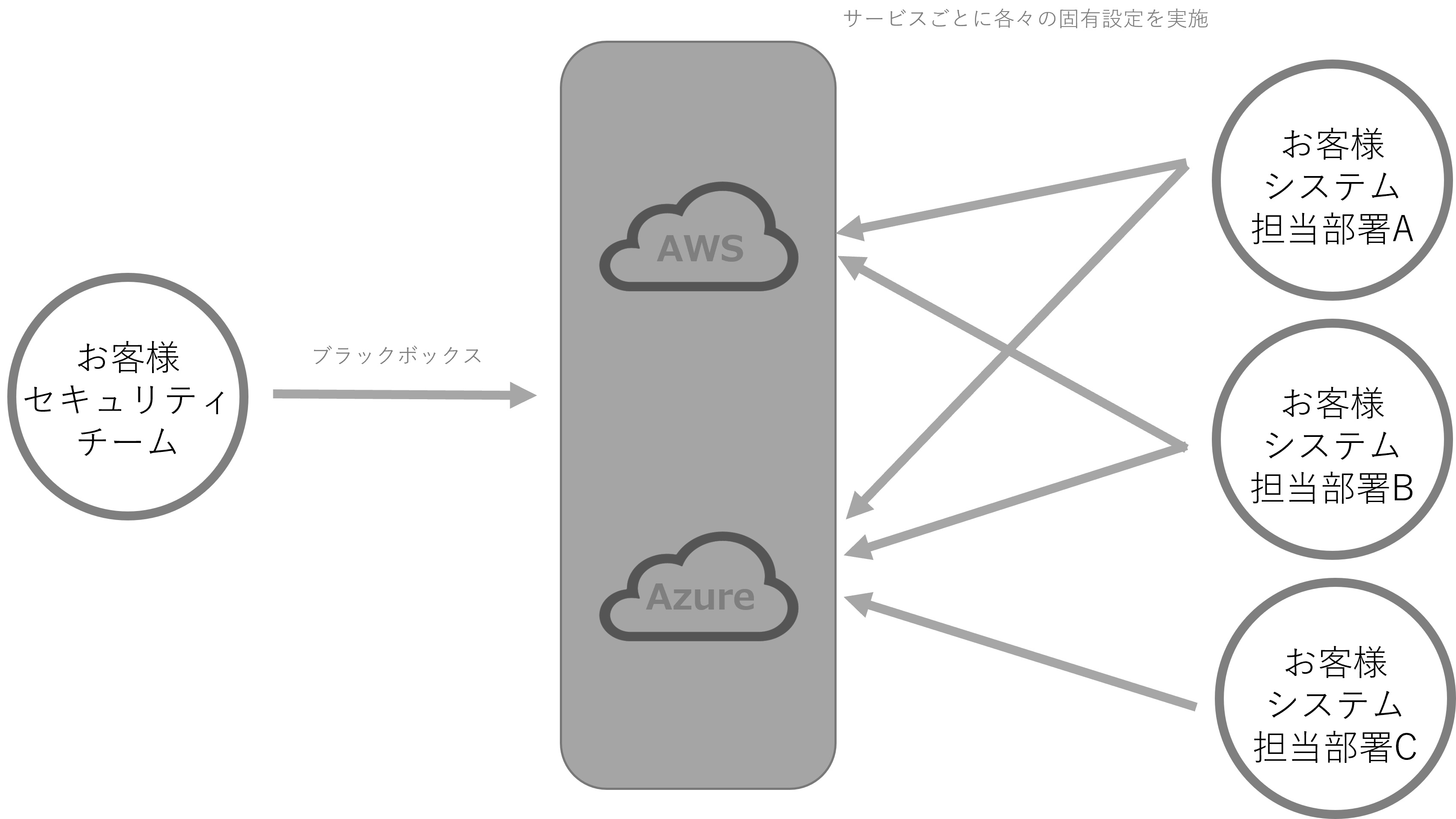
The security policy has not been established, but there is a need to understand the configuration status of resources in AWS and Azure. Currently, AWS and Azure are black boxes, and not understood the configuration and the risks involved. We also have concerns about operations and would like assistance.
It is now possible to identify configuration setting errors in AWS and Azure, which had previously been black boxed.
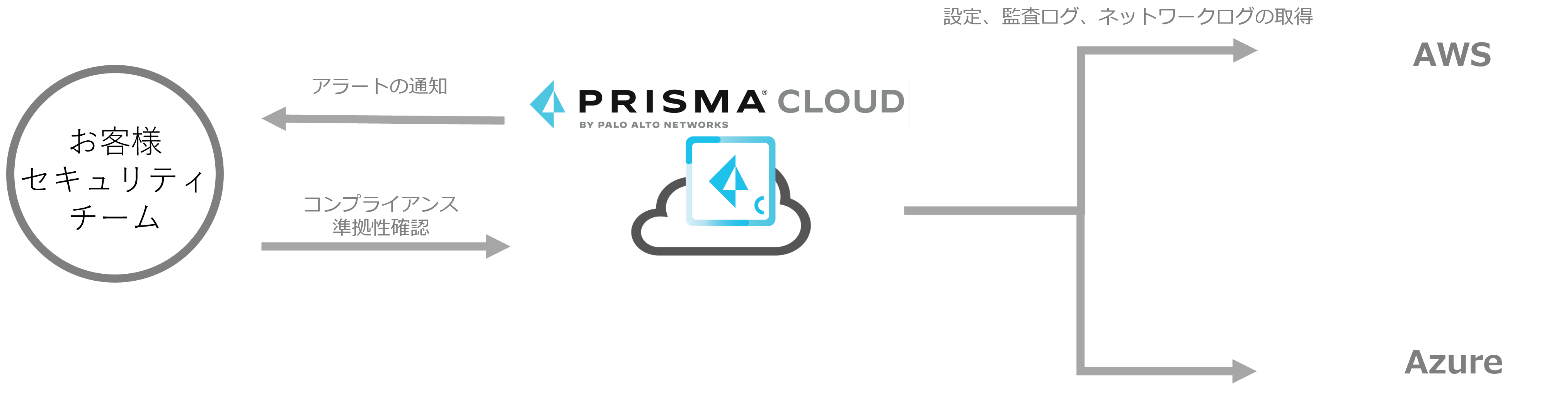
Through the development of standard policies for Prisma Cloud and custom policies in IdealRoute Consulting, the company gained a foothold in developing a security policies for the cloud.
The company was able to grasp once again the benefits of implementing the product and clearly understand the roadmap for future in-house operations, enabling it to move forward with plans for a more full-scale company-wide deployment.
We had already established our own security policy, but when it came to select a product to implement the policy, there is a concern of how flexibly the security policies can be applied. Through the POC, the company was able to determine how the security policy could be applied and the basic operations such as how violations of the security policy would be detected, was well identified.
The POC also gave us a clear picture of basic operations with various advice on corrective measures to be taken after an alert is generated.